These IT Threats Can Ruin Your Business
Technology is a major part of today’s business. It’s fair to say anyone that works in business today is at least semi-proficient with the technology needed to complete their tasks. Unfortunately, for many people, however, the fact that their business requires complicated technology is problematic. This is because at any given moment there are people looking to undermine their job, seeking access to accounts that will allow them to siphon money and data from organizations.
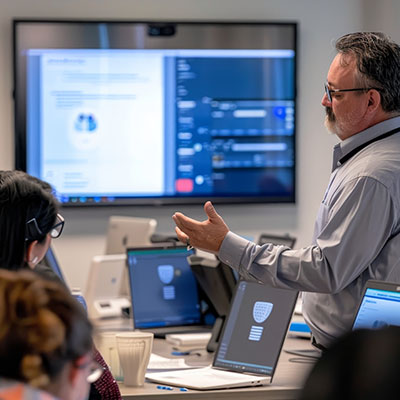
This is why cybersecurity training is so important to businesses today. With so many threats looking to get into so many access points, the workers’ knowledge on how to keep attackers at bay becomes critical. In this month’s newsletter, we go into some of the things that need to happen to ensure that your business’ IT network is secure and how to drill into your staff’s consciousness their role in protecting it.
What are the Threats?
There are so many threats that there is no way to effectively explain them all in this article, but this month, we give you a structured approach to cover key areas:
Start with Identifying Risks
You need to level with your employees: there are a lot of threats out there. Most start with phishing. Phishing is the act of scamming people to provide information that will allow cyberattackers to gain access to protected accounts, allowing scammers to siphon data, steal money, and further complicate your business’ IT. You will want to lay the threats out simply so that people understand their roles in securing your network and infrastructure. Here are a few talking points you want to address:
- Create strong passwords – Teach the importance of creating strong, unique passwords and using password managers.
- Keep software updated – Emphasize the need to update software and systems to patch vulnerabilities.
- Training on identifying potential threats – Provide instruction on verifying the legitimacy of emails and links before clicking.
- Use cybersecurity tools – Tools such as antivirus, anti-malware, firewalls, VPNs, and multi-factor authentication can work to enhance your security posture.
- Use encryption – Encrypting sensitive information both in transit and at rest can go a long way toward keeping data secure
- Following policies – You’ll want to create comprehensive security policies and ensure that your staff follows them closely.
- Further testing and training – Threats change and you will want to make sure your staff has the information needed to actively participate in your cybersecurity initiatives.
You need your staff to help keep your organization’s digital assets secure. For more information about keeping your business secure online, call White Mountain IT Services today at (603) 889-0800.

