Recent Blog Posts
Technology is a major part of today’s business. It’s fair to say anyone that works in business today is at least semi-proficient with the technology needed to complete their tasks. Unfortunately, for many people, however, the fact that their business requires complicated technology is problematic. This is because at any given moment there are people looking to undermine their job, seeking access to accounts that will allow them to siphon money and data from organizations.
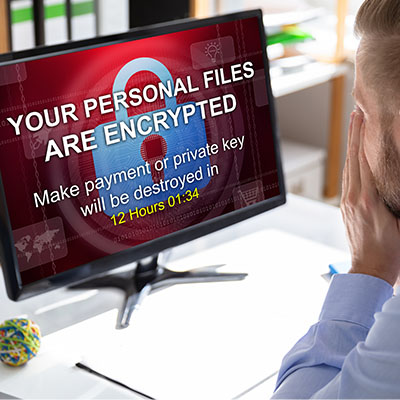
We’ve spent the last few weeks discussing ransomware’s impacts on different subsets. First, we discussed how a ransomware attack impacts the customers of the infected business, and then we touched on the infected business itself. To end, we want to touch on ransomware’s impacts on society, specifically regarding economic health and geopolitical security, known as third-order harms.
Data is extremely important in the way that most businesses conduct themselves. This results in other people wanting that information, too. Today’s blog will look at how seemingly everyone online is out for your data.
Have you ever heard of the “man-in-the-middle” attack or MitM? It’s a situation where your data is stolen by an onlooker who situates themselves in the right place at the right time. Data interception is a very real thing that your business should be prepared to fight against. Let’s discuss some strategies you can use to counter these sneaky attacks.
Last week, we discussed the many impacts your business suffering from ransomware has on “second-order harm,” downstream businesses, and average, ordinary people. This time, we wanted to return to “first-order harms”… those the impacted business has to deal with itself.